A new report says that the passwords we use on a daily basis should require a supplemental step. With e-mail, Facebook, Twitter, Instagram and all of the other passwords tech users are required to remember things can get pretty complicated, especially if you have ever used “password” as your actual password.
“It’s time for a change. Passwords alone can’t hack it. There is widespread consensus among data security experts that using only passwords is poor security, and there are readily available alternatives,” said Daniel J. Solove and Woodrow Hartzog of Wired.
“Yet the lone password has been used for authentication for so long and so widely that it is difficult to change the status quo, even if many wished to.”
Solove and Hartzog said that the problem is people are asked to commit a password to memory and then change it frequently. For some it just doesn’t work and that’s where passwords that actually have the word “password” as the security code start popping up. They even brought up the fact that people still write their passwords on sticky notes near their computers or scrap paper making it perfectly easy for someone else to easily hack into their accounts. For this matter, both Solove and Hartzog recommend adding a factor.
“There are other methods of authentication that can be used that avoid the problems with passwords—and many are relatively cheap and easy to deploy,” according to the report.
“One such example is two-factor authentication. The essence of two-factor authentication is simple. In order to login, you must have something you know (usually a password), as well as one additional factor, usually something you have (usually your cellphone). Additional factors could be mixed and matched to avoid relying on the sole password.”
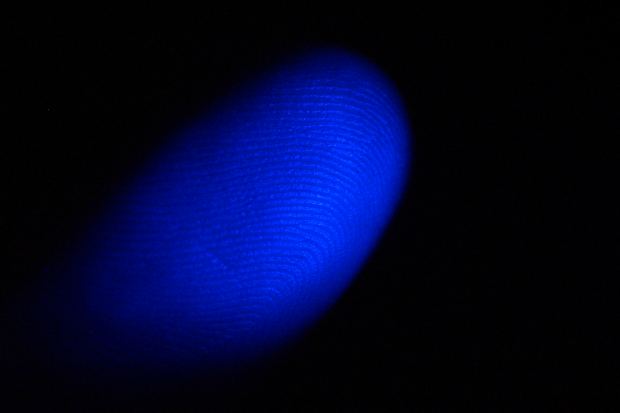
Other supplements such as “having a friend vouch for you, signing your name, or biometric identifiers like your face, fingerprints, or iris,” were also suggested by the team. It’s a matter of how important the information is to the user, do they want to jump through extra loops to access that information?
Read the full story.

